Why Manufacturers Are Moving Beyond the Purdue Model to IEC 62443
The rapid evolution of cybersecurity threats and the increasing complexity of industrial control systems (ICS) have pushed manufacturing and ICS industries to rethink their cybersecurity frameworks. While the Purdue Enterprise Reference Architecture (Purdue Model) has been a foundational approach to organizing industrial networks, the adoption of IEC 62443, a globally recognized cybersecurity standard, is gaining momentum. This shift is driven by the need for dynamic, flexible, and comprehensive security measures that address modern-day threats and comply with emerging regulations.
Regulations Encouraging IEC 62443 Adoption
Several global regulations and initiatives are driving the shift toward IEC 62443 compliance:
NIST Cybersecurity Framework (CSF): In the U.S., NIST CSF emphasizes risk-based security strategies, aligning well with IEC 62443’s principles.
EU NIS2 Directive: The European Union’s NIS2 Directive mandates stringent cybersecurity measures for critical industries, encouraging alignment with standards like IEC 62443.
ISA/IEC 62443 Certification Requirements: Many industrial buyers now require vendors to demonstrate compliance with IEC 62443 as a prerequisite for partnerships.
Cybersecurity Executive Orders: U.S. federal directives targeting critical infrastructure security increasingly advocate for adopting international standards like IEC 62443.
Overview of the Purdue Model
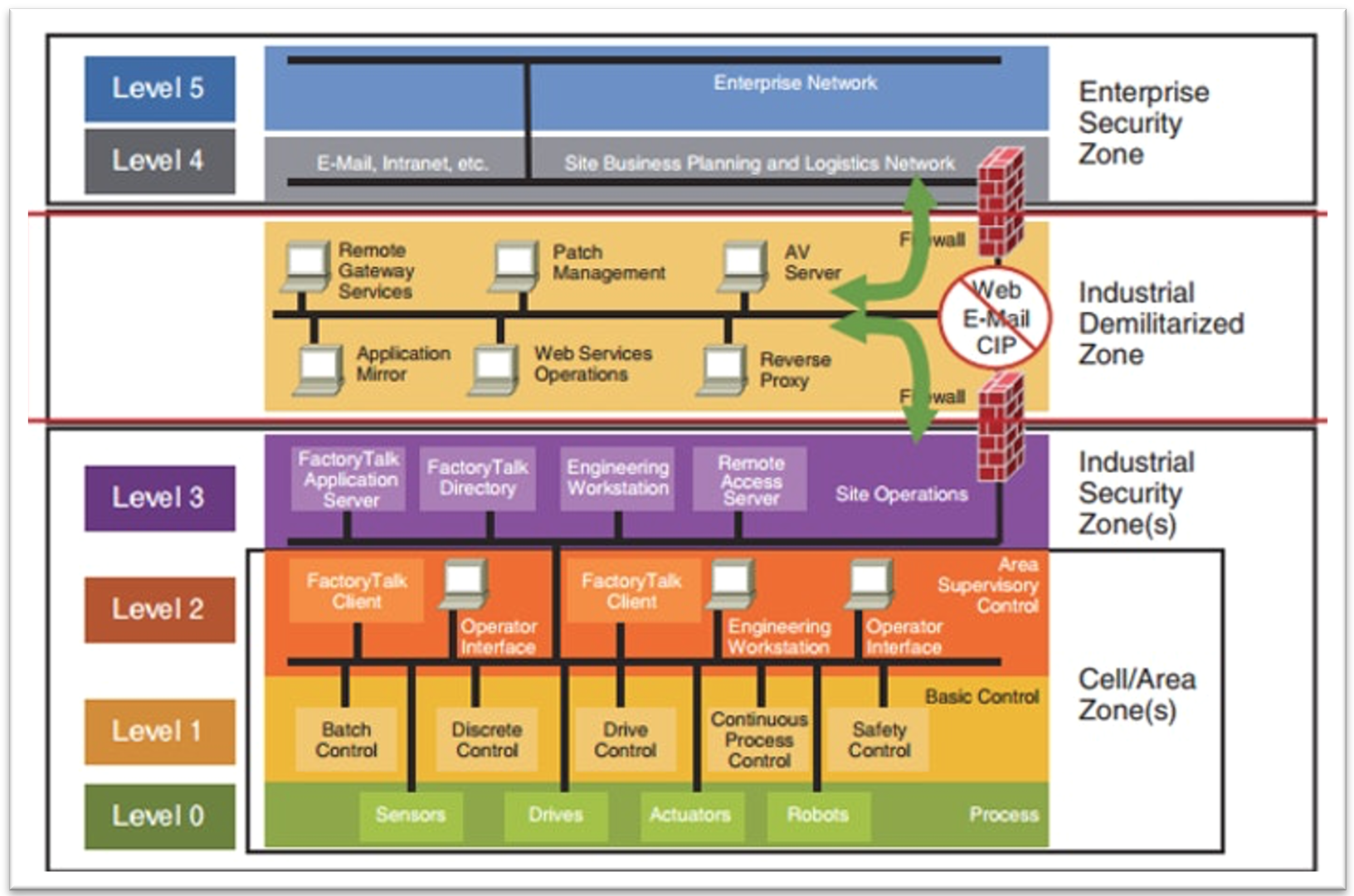
Purpose: The Purdue Enterprise Reference Architecture (PERA) defines a hierarchical model for organizing and securing Industrial Control Systems (ICS) and Operational Technology (OT).
Structure: It segments an industrial environment into levels (e.g., enterprise, operations, supervisory, control, and physical processes).
Limitations:
Static Nature: Assumes clear boundaries between levels, which may not align with modern interconnected systems.
Cybersecurity Gaps: Designed for operational efficiency, not inherently for cybersecurity.
Flat Networks: Often results in limited segmentation, making lateral movement by attackers easier.
Introduction to IEC 62443
Purpose: IEC 62443 is a global standard for cybersecurity in IACS, addressing risks from both external and internal sources.
Scope: Focuses on security throughout the system lifecycle (design, implementation, operation, and maintenance).
Key Features:
Risk-Based Approach: Considers diverse threats and vulnerabilities specific to IACS environments.
Defense-in-Depth: Emphasizes layered security mechanisms across systems and zones.
Roles and Responsibilities: Defines roles for asset owners, integrators, and component suppliers to ensure accountability.
Granularity: Applies to individual devices, systems, and networks, supporting modular security controls.
Key Aspects & Advantages of IEC 62443
IEC 62443, developed by the International Electrotechnical Commission, provides a robust, risk-based approach to securing ICS environments. Its adoption offers several advantages:
Security by Design: Unlike the Purdue Model, IEC 62443 embeds cybersecurity throughout the system lifecycle, from design to operation.
Zone and Conduit Model: It introduces the concept of zones (areas with similar security requirements) and conduits (secured communication paths), offering a more flexible approach to segmentation.
Risk Management: IEC 62443 prioritizes risk assessment and mitigation strategies tailored to individual environments.
Vendor Neutrality: It provides guidelines for both asset owners and solution providers, fostering collaboration and ensuring uniform security standards.
Reasons for the Shift
Evolving Threat Landscape: Increased connectivity (e.g., IIoT, cloud-based systems) expands attack surfaces. Sophisticated cyberattacks target legacy systems that rely on Purdue’s flat networks.
Need for Flexibility: Modern industrial systems blur boundaries between traditional Purdue levels. IEC 62443 accommodates diverse architectures, including converged IT-OT networks.
Compliance and Standards: Regulatory frameworks and industry best practices increasingly reference IEC 62443 for cybersecurity.
Implications for Transition
Restructuring Networks: Implement zones and conduits to replace static Purdue levels. Enhance segmentation to limit lateral movement.
Adopting Risk Management: Conduct risk assessments for assets, processes, and systems. Prioritize controls based on threat likelihood and impact.
Lifecycle Security: Design systems with security built-in (not bolted on later). Regularly update and maintain security controls.
Stakeholder Collaboration: Coordinate among asset owners, system integrators, and vendors. Clearly define security responsibilities and accountability.
Implementing Standards: Align policies and procedures with IEC 62443 requirements. Leverage certification programs to validate compliance.
Practical Steps for Transition
Step 1: Gap Analysis
Evaluate existing systems based on Purdue and IEC 62443 requirements.
Identify vulnerabilities and areas requiring updates.
Step 2: Create Transition Plan
Establish goals for aligning with IEC 62443.
Prioritize high-risk zones and assets.
Step 3: Redesign Network Architecture
Replace flat or hierarchal networks with segmented zones and conduits.
Use firewalls, intrusion detection systems, and secure gateways.
Step 4: Implement Defense-in-Depth Architecture
Apply security controls at multiple levels: physical, network, system, and application.
Step 5: Continuous Monitoring and Improvement
Establish monitoring systems to detect and respond to threats.
Regularly update policies, procedures, and technologies.
The Way Forward
The shift from the Purdue Model to IEC 62443 represents a fundamental transformation in how manufacturing and ICS environments approach cybersecurity. As threats grow more sophisticated, organizations must prioritize security frameworks that provide adaptability, scalability, and compliance with global regulations. IEC 62443 not only addresses the limitations of the Purdue Model but also establishes a foundation for resilient, future-proof industrial systems. The benefits for IEC 62443 adotion include but are not limited to:
Improved resilience against cyber threats.
Enhanced compliance with global regulations and standards.
Greater interoperability in modern industrial environments.
Clear accountability across the system lifecycle.
By embracing IEC 62443, manufacturers and industries can ensure operational continuity while staying ahead of evolving cybersecurity challenges. This transition is no longer optional—it’s a necessity in the modern era. By adopting IEC 62443, organizations can future-proof their industrial systems against evolving cybersecurity challenges, surpassing the static and limited capabilities of the Purdue Model.