Securing Smart Manufacturing: Navigating Cyber Risks in the Industry 4.0 to 5.0 Transition
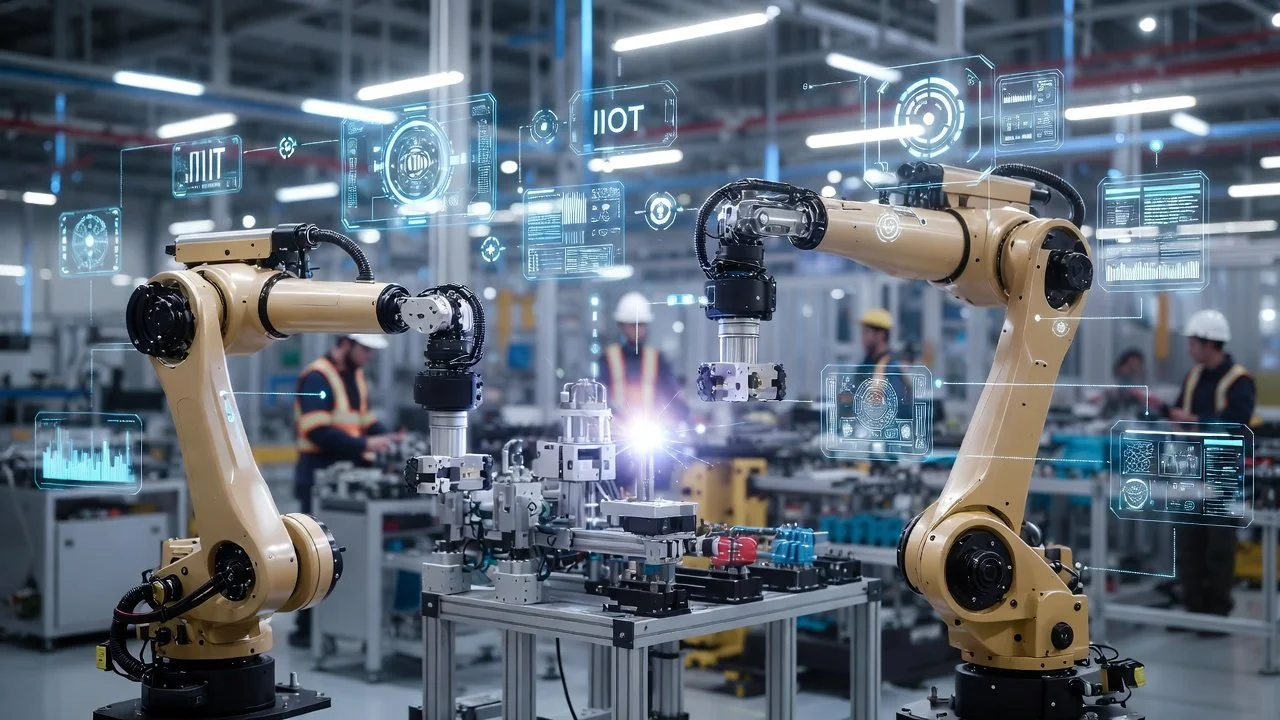
The manufacturing industry is advancing rapidly through Industry 4.0 technologies — smart factories, IoT connectivity, digital twins, and advanced automation — while many organizations are already incorporating Industry 5.0 principles. Industry 5.0 emphasizes human-centric design, resilience, sustainability, and meaningful collaboration between people and intelligent systems.
This evolution creates powerful opportunities, but it also significantly expands the attack surface. Manufacturers must manage complex IT/OT convergence, secure critical manufacturing processes, safely integrate AI into operational technology (OT) environments, and defend against rising ransomware and supply-chain threats. In 2025, manufacturing was one of the most targeted sectors for cyberattacks globally.
Professional services in cybersecurity, data governance, IT/OT advisory, and cyber assurance are essential to protect operations while enabling secure, sustainable innovation.
1. Automotive Manufacturing
Key Challenge: Protecting intellectual property in autonomous and electric vehicle technologies while securing global supply chains and meeting supplier requirements.
Cybersecurity, data governance, and IT/OT advisory support connected production lines.
Cyber assurance includes alignment with ISO/SAE 21434 and TISAX for suppliers.
2. Pharmaceutical Manufacturing
Key Challenge: Ensuring data integrity, regulatory compliance, and protection against production-disrupting ransomware.
Services focus on ransomware defense, FDA/GMP compliance, and safe IoT integration for real-time monitoring and predictive maintenance.
3. Aerospace and Defense (A&D) Manufacturing
Key Challenge: Safeguarding sensitive national security-related data and critical infrastructure while managing complex supply chains.
Services deliver zero-trust architectures and secure IT/OT convergence. (We will cover CMMC and government contracting in detail in upcoming articles.)
4. Consumer Goods Manufacturing
Key Challenge: Balancing high-efficiency production with protection of customer and operational data in an e-commerce-driven market.
Services provide network segmentation, GDPR/CCPA compliance, and smart factory alignment.
5. Heavy Machinery Manufacturing
Key Challenge: Maintaining uptime and security for IoT-connected machinery and complex manufacturing processes.
Services address legacy systems, predictive maintenance, and secure interoperability in autonomous and AI-augmented production processes.
The Critical Role of OT-Specific Vulnerability Management
As IIoT adoption accelerates, OT and ICS environments are becoming deeply integrated with enterprise IT and cloud platforms. A single vulnerability in a SCADA system or PLC can now be exploited from the corporate network, leading to costly downtime or safety risks.
Traditional IT vulnerability management tools often rely on active scanning and high-bandwidth queries that can disrupt real-time control systems. In contrast, purpose-built OT vulnerability management solutions use passive monitoring to discover assets, understand ICS-specific protocols (Modbus, DNP3, OPC UA, etc.), and prioritize risks based on actual operational impact rather than generic CVSS scores.
Professional services help manufacturers implement the right OT-focused approach alongside their enterprise tools, delivering unified visibility and safe remediation without risking production availability.
Why Professional Services Matter
The stakes in manufacturing have never been higher. Cyber threats, complex regulatory requirements, and the need for secure digital integration demand specialized expertise. By working with experienced professionals in cybersecurity, data governance, IT/OT advisory, and cyber assurance, manufacturers can protect intellectual property, achieve compliance (including TISAX for suppliers), safely integrate automation and AI, and build genuine resilience against disruptions.
As the industry continues its transition toward smarter, more human-centric production under Industry 5.0, having the right guidance becomes increasingly critical to turn innovation into a sustainable competitive advantage.
Sources
ANSI/ISA-62443-2-1 Edition 2 (2024) and ISA-TR62443-2-2-2025 (December 2025)
NIST SP 800-82 Rev. 3 (current) and Rev. 4 pre-draft (January 2026)
CISA et al., “Principles for the Secure Integration of Artificial Intelligence in Operational Technology” (December 3, 2025)
Google DeepMind, “Intelligent AI Delegation” (arXiv:2602.11865, February 12, 2026)
IBM X-Force Threat Intelligence Index 2026
ENX Association – TISAX Requirements (2025–2026)
Relevant Frameworks and Regulations
-
Automotive manufacturers handle sensitive IP related to autonomous vehicles and connected systems, making compliance essential to protect against espionage and cyberattacks.
ISO/SAE 21434: A critical standard for automotive cybersecurity, covering risk management, engineering processes, and organizational structures.
UNECE WP.29 R155 and R156: Mandates cybersecurity and software update management systems for vehicles in the EU.
GDPR (General Data Protection Regulation): Relevant for protecting customer data collected through connected vehicles or customer interactions.
TS 16949: Focuses on quality management in the automotive supply chain, often including cybersecurity as part of supplier assessments.
TISAX (Trusted Information Security Assessment Exchange): A framework designed for assessing and exchanging information security standards specifically within the automotive industry and its supply chain, ensuring compliance with industry-specific requirements like data protection and intellectual property security.
NIST Cybersecurity Framework (CSF): A voluntary framework adopted by many automotive manufacturers to improve security posture.
-
Pharmaceutical companies face strict regulatory environments to ensure product safety, data integrity, and privacy protection, requiring adherence to multiple overlapping frameworks.
FDA 21 CFR Part 11: Governs electronic records and signatures, ensuring the integrity of digital data in pharmaceutical processes.
HIPAA (Health Insurance Portability and Accountability Act): Protects patient data in pharmaceutical companies involved in clinical trials or healthcare.
GDPR and CCPA: Regulate the handling of personal data for patients or clinical trial participants globally and in California, respectively.
GAMP 5 (Good Automated Manufacturing Practice): Provides guidance for validating automated systems to meet regulatory expectations.
NIST SP 800-53: Establishes security and privacy controls, particularly for pharmaceutical companies working with government agencies.
-
With national security implications, A&D manufacturers must comply with stringent cybersecurity requirements to protect sensitive data and meet government contract obligations.
NIST SP 800-171: Focuses on protecting Controlled Unclassified Information (CUI) in non-federal systems.
CMMC (Cybersecurity Maturity Model Certification): A critical framework for contractors working with the U.S. Department of Defense (DoD), ensuring cybersecurity readiness.
ITAR (International Traffic in Arms Regulations): Regulates the handling and sharing of defense-related data.
DFARS (Defense Federal Acquisition Regulation Supplement): Specifies cybersecurity requirements for defense contractors and subcontractors.
ISO 27001: A global standard for information security management systems (ISMS), often adopted by A&D manufacturers.
-
Consumer goods manufacturers must safeguard customer data, maintain supply chain integrity, and ensure compliance with privacy regulations.
GDPR and CCPA: Govern the protection of consumer data, particularly in e-commerce and personalized product manufacturing.
ISO 27001: Ensures the security of data systems managing consumer information and business operations.
NIST CSF: Offers guidance for improving cybersecurity posture and mitigating risks.
PCI DSS (Payment Card Industry Data Security Standard): Applies to manufacturers processing payments directly through online platforms.
ISO 22301 (Business Continuity Management): Supports operational resilience in case of cyber incidents or supply chain disruptions.
-
The heavy machinery sector relies on IoT and Industrial Control Systems (ICS), which are prime targets for cyberattacks that could disrupt operations or compromise sensitive data.
IEC 62443: A global standard for industrial automation and control system cybersecurity, applicable to IoT-connected machinery.
ISO 27001: Provides a framework for securing information systems used in production and machinery management.
NERC CIP (Critical Infrastructure Protection): Relevant for manufacturers producing equipment for critical infrastructure sectors, ensuring compliance with cybersecurity standards.
GDPR and Regional Privacy Laws: Apply to personal data collected from customers or employees, particularly in IoT-enabled services.
NIST CSF and SP 800-82: SP 800-82 provides specific guidelines for securing Industrial Control Systems (ICS), which are core to heavy machinery operations.
-
ISO 27001: Universal for managing information security in IT/OT systems.
GDPR and Regional Privacy Laws: Crucial for any manufacturer collecting, processing, or storing personal data.
NIST CSF: Widely adopted for improving cybersecurity resilience and aligning with best practices.
SOC 2: Helps assess data security, availability, and confidentiality, especially for third-party audits.
COBIT (Control Objectives for Information and Related Technologies): A governance framework ensuring alignment between IT and business goals.